If you've ever wondered how Bitcoin or Ethereum manage to keep your transactions safe without a central authority, the answer often boils down to a clever data structure called the Merkle tree. It's not just academic jargon—it's the backbone that lets you trust a crypto exchange's balance sheet or verify a block without downloading the entire blockchain. I've seen projects fail because they messed up their Merkle tree implementation, thinking it was just a minor detail. Let's cut through the noise and see why this matters.
What You'll Learn in This Guide
What is a Merkle Tree? A Simple Analogy
Imagine you have a huge list of transactions—say, 10,000 of them—and you want to prove that one specific transaction is part of that list without showing the whole thing. A Merkle tree lets you do that efficiently. It's a binary tree of cryptographic hashes, named after Ralph Merkle who proposed it in 1979. In plain English, it's a way to summarize data so you can check its integrity quickly.
Here's a personal touch: I once audited a small crypto exchange that claimed to use Merkle trees for proof-of-reserves. Turns out, they were just hashing data randomly without building the tree properly. That's a red flag. A proper Merkle tree isn't about complexity; it's about organizing hashes in a tree structure where each leaf node is a hash of a data block, and each non-leaf node is a hash of its children. The root hash at the top represents the entire dataset.
Key Point: Merkle trees are foundational for systems where data needs to be verified without full disclosure, like in blockchain or peer-to-peer networks. They're not an encryption method—they're about data integrity.
How Does a Merkle Tree Work? Step-by-Step Breakdown
Let's walk through how you'd build one. Suppose you have four transactions: TxA, TxB, TxC, and TxD. Here's the process:
- Hash the data: Compute cryptographic hashes (like SHA-256) for each transaction. Call them HashA, HashB, HashC, HashD.
- Pair and hash: Combine HashA and HashB, then hash them to get HashAB. Do the same for HashC and HashD to get HashCD.
- Final root: Hash HashAB and HashCD together to produce the Merkle root, say HashABCD.
This root hash is what gets stored in the blockchain block header. If any transaction changes, the root hash changes, alerting everyone to tampering. The beauty is in verification: to prove TxA is in the tree, you only need HashB, HashCD, and the root, not all transactions. That's called a Merkle proof.
I remember helping a friend set up a light wallet for Bitcoin. He was skeptical—how can you trust a summary? I showed him that with a Merkle proof, the wallet downloads just a few hashes instead of gigabytes of data. It's like checking a receipt against a total sum; if the numbers don't add up, something's wrong.
| Step | Action | Example Output (Simplified) |
|---|---|---|
| 1. Data Input | Transactions TxA, TxB, TxC, TxD | Raw data blocks |
| 2. Leaf Hashes | Hash each transaction with SHA-256 | HashA, HashB, HashC, HashD |
| 3. Intermediate Hashes | Pair and hash leaves | HashAB = hash(HashA + HashB), HashCD = hash(HashC + HashD) |
| 4. Merkle Root | Hash intermediate hashes | HashABCD = hash(HashAB + HashCD) |
Merkle Trees in Blockchain: Real-World Applications
In blockchain, Merkle trees are everywhere. Bitcoin uses them to bundle transactions into blocks. Ethereum takes it further with Merkle Patricia trees for state management. But let's get practical—how does this affect you as a user or developer?
First, for crypto exchanges. When an exchange like Binance or Coinbase does a proof-of-reserves audit, they often publish a Merkle root of customer balances. This allows users to verify their funds are included without revealing everyone's balance. It's a trust mechanism. However, I've noticed a pitfall: some exchanges only publish the root without providing tools for verification, making it useless. Always check if they offer Merkle proof generators.
Second, for light clients. These are wallets that don't store the full blockchain. They rely on Merkle proofs to validate transactions. Without Merkle trees, light clients would be impossible, forcing everyone to run heavy nodes. That's a scalability win.
Third, in decentralized finance (DeFi). Smart contracts on Ethereum use Merkle proofs for airdrops or whitelisting. For instance, a project might distribute tokens based on a Merkle tree of eligible addresses, reducing gas costs. I worked on a DeFi project where we messed this up initially—we didn't update the tree properly, causing disputes. Lesson learned: always test tree updates thoroughly.
Why Merkle Trees Beat Simple Hashing
You might ask, why not just hash all transactions together? Well, with a simple concatenated hash, to verify one transaction, you'd need all data. Merkle trees cut that down to logarithmic complexity. For 1 million transactions, a Merkle proof requires about 20 hashes, while a naive approach needs all 1 million. That's efficiency.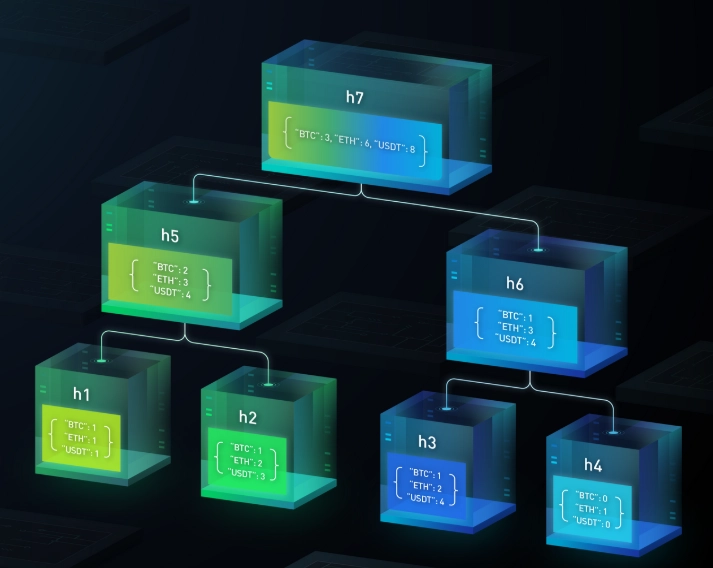
Case Study: Bitcoin's Merkle Tree in Action
Let's dive into Bitcoin, since it's the most famous example. Each Bitcoin block contains a Merkle root in its header. Here's how it works in practice:
When miners create a block, they gather transactions from the mempool. They arrange them in a Merkle tree, compute the root, and include it in the block header. This root is then hashed with other header data to form the block hash. If you're running a full node, you verify all transactions, but for a light client, it's different.
Say you want to check if a transaction is confirmed. Your light client asks a full node for a Merkle proof. The node provides the relevant hashes (like HashB and HashCD from our earlier example) and the root. Your client computes locally and matches it with the root in the block header. If it matches, the transaction is valid.
I recall a bug in an early Bitcoin implementation where an odd number of transactions caused issues with tree construction. It led to forks. That's why most systems use balanced trees or pad data. These nuances matter—it's not just about following a recipe.
Bitcoin's design also allows for pruning: old transactions can be discarded once the Merkle root is verified, saving storage. This is crucial for long-term scalability.
Common Misconceptions and Pitfalls to Avoid
After years in crypto, I've seen people get Merkle trees wrong. Here are the top mistakes:
- Merkle trees aren't for encryption: They don't hide data; they ensure integrity. If you need privacy, look at zero-knowledge proofs.
- Root alone isn't enough: Publishing a Merkle root without accessible proofs is like having a lock with no key. Exchanges should provide verification tools.
- Tree construction errors: Using the wrong hash function (e.g., MD5 instead of SHA-256) or mishandling odd numbers of leaves can break security. Always use cryptographically secure hashes.
- Assuming it's foolproof: Merkle trees prevent tampering but don't stop all attacks. For example, if an attacker controls the data source, they can create a valid tree for fraudulent data. That's why decentralization matters.
One project I advised used Merkle trees for supply chain tracking. They thought it would magically prevent fraud, but without proper data input controls, it was garbage in, garbage out. Merkle trees verify consistency, not truth.
FAQ: Your Burning Questions Answered
Wrapping up, Merkle trees are more than a blockchain buzzword. They're a practical tool for ensuring data integrity in decentralized systems. Whether you're a trader verifying exchange reserves or a developer building a new protocol, understanding how they work can save you from costly mistakes. Don't just take my word for it—try building a simple Merkle tree in code; it's the best way to see the magic firsthand. And remember, in crypto, trust is built, not given, and Merkle trees are one brick in that foundation.
Reader Comments